Some of your programs won’t respond until they receive a signal via the Internet. If you have a program that doesn’t poke its own hole through the Windows Firewall, you can tell the firewall to allow packets destined for that specific program — and only that program — in through the firewall.
Choose Start→Control Panel. Click the System and Security link; click Windows Firewall.
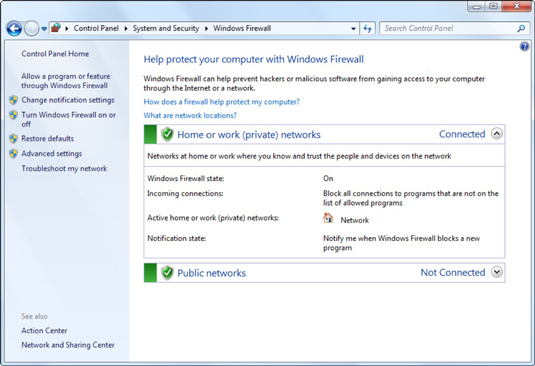
You see the main Windows Firewall control window.
On the left, click the link labeled Allow a Program or Feature through Windows Firewall.
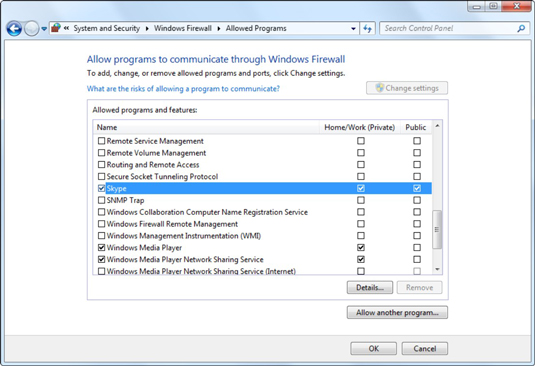
Windows Firewall presents you with a lengthy list of programs: If a box is checked, it means that Windows Firewall will allow incoming packets of data directed to that program.
The list varies depending on whether you’re connected to a home or work network (a private network) or a public network. There are many programs that won’t be allowed to receive unsolicited packets on a public network, such as Windows Media Player.
Select the program’s check box depending on the type of network you want to be connected to when you allow the unsolicited incoming data.
It’s rare indeed that you would allow access when connected to a public network but not to a home or work network.
If you can’t find a program, click the Change Settings button at the top and then click the Allow Another Program button at the bottom.

Windows Firewall goes out to all common program locations and finally presents you with a list of available programs. It can take a while.
If you still don’t see the program you want, click the Browse button and locate the program. Select it and click Open.
The program you chose appears on the Add a Program list.
Choose the program you want to add and click the Add button.
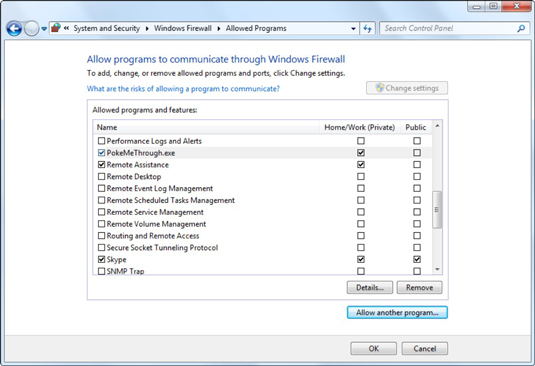
The Allow Programs list reappears with you program added. For this example, we added a program called PokeMeThrough.exe.
Realize that you’re opening a potential, albeit small, security hole. If you authorize a renegade program to accept incoming packets, the bad program could let the fox into the chicken coop.
Select the check boxes for your poked-through program. Then Click OK.
Your poked-through program can immediately start handling inbound data.





