If you’re working with a personal (that is, non-work) computer, managing these settings is your responsibility. But if you’re using a work computer, you may find that your employer’s IT department is already enforcing some of these settings according to its security policy. Those settings will appear grayed-out and with a little buildings icon next to it, meaning that you can’t change them.
Here’s a rundown of what all those content privacy settings mean.Cookies
Cookies allow external websites to store information on your computer to help them remember you. This information may include the last time you visited the site, the links you’ve clicked, and so on. You may not want external websites to set that kind of data on your computer, or your employer may not want them to. Just check the box to block third-party cookies and site data if you don’t want websites to have that kind of access.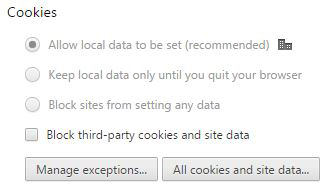 Figure 1: You can block websites from setting cookies on your computer.
Figure 1: You can block websites from setting cookies on your computer. Source: Google.com
Images
Deciding whether to show images on websites isn’t really a security concern, but not showing images can speed up your browsing considerably. You’ll miss out on a lot, though. You may only want to disable images if your connection is very slow or if you’re on a data plan (for example, if you’re on the road and tethering your laptop to your phone’s data connection so that you can access the internet). Downloading images can eat into your allowed data quickly, and if you’re interested only in the text, why waste your data?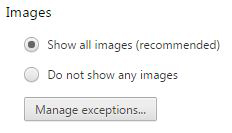 Figure 2: No more pretty pictures, please.
Figure 2: No more pretty pictures, please. Source: Google.com
JavaScript
JavaScript can be a major security concern. JavaScript applications are tiny programs that run on websites. Most above-board websites use JavaScript in a positive, nonthreatening way, such as gathering website traffic data (that is, tracking where you go and what you click on their website).However, some not-so-nice websites can use JavaScript to try to get at the information on your computer. If you’re in the habit of visiting only nice websites, then you can leave JavaScript enabled; however, if you tend to venture on the wild side of the web, you may want to disable JavaScript.
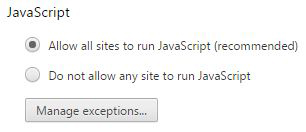 Figure 3: Disable JavaScript if you don’t want to risk intrusion.
Figure 3: Disable JavaScript if you don’t want to risk intrusion. Source: Google.com
Handlers
Handlers are external applications (that is, not your browser) on your computer that are allowed to handle certain tasks. For example, if you click a link for someone’s email address, it’s very likely that Chrome will tell your default email application to open so that you can write a new message to the recipient. Websites may ask you if you’d like them to handle certain tasks for you. It’s up to you to decide whether to let them. Rest assured, websites can’t do this without your permission, which is why they ask.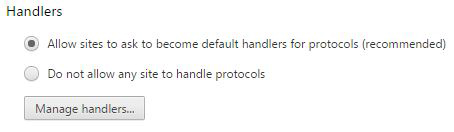 Figure 4: Let other apps do the heavy lifting.
Figure 4: Let other apps do the heavy lifting. Source: Google.com
Plugins
Plugins are little applications that you install in your browser to enhance its functionality. You might also call then Add-ons. Plugins are a great way to enable your browser to do things more easily. For example, if you frequently take screenshots of websites, you can get a screenshot plugin that enables you to take a screenshot with just one or two clicks. But plugins can also do some nefarious things, which is why you may want to limit their use.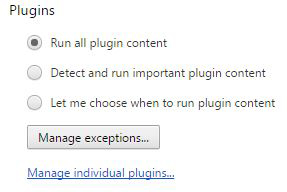 Figure 5: Plug in and expand Chrome’s functionality.
Figure 5: Plug in and expand Chrome’s functionality. Source: Google.com
Pop-ups
We all know about pop-ups — those mostly annoying browser windows that pop up with advertisements, interrupting the flow of what you’re doing. It’s worse than TV commercials! Sometimes, though, pop-ups are necessary, such as when you’re purchasing something online. But that’s a relatively rare situation compared to when ads pop up, so it’s best to keep pop-ups disabled and add exceptions on a case-by-case basis.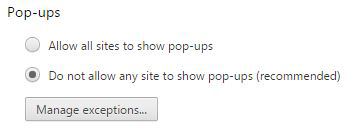 Figure 6: Get out of here, dreaded popup ads.
Figure 6: Get out of here, dreaded popup ads. Source: Google.com
Location
Some websites may want to know where you’re located, such as a shopping site asking you where you are so that it can show you pricing for the nearest store. Most of the time, this is harmless. But still, you may not want people to know where you are. So, it’s probably best to not allow websites to know where you are, except for when they ask and you decide to let them know. Note, though, that for your work computer, your IT department may completely disable this so that, no matter what, websites can’t know where you are.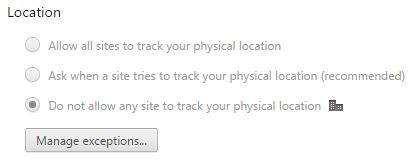 Figure 7: Don’t let them know where you are.
Figure 7: Don’t let them know where you are. Source: Google.com
Notifications
Chrome allows websites to provide desktop notifications, such as when new emails arrive in your web-based email app or the latest football scores or weather updates. The default for this setting is to have websites ask if you want to receive notifications. But if you know for sure that you either want or don’t want them, you can change this setting appropriately. Figure 8: Get notified by websites.
Figure 8: Get notified by websites. Source: Google.com
Fullscreen
Believe it or not, some websites have the audacity to want to take over your entire screen. Luckily, Chrome makes them ask first, so you can rightfully say no. You can use this setting to specify exceptions — that is, sites that you want to automatically take over your screen, such as gaming sites. Figure 9: Manage which websites can take over your computer screen.
Figure 9: Manage which websites can take over your computer screen. Source: Google.com
Mouse cursor
You may not realize this, but an external website can disable your mouse cursor if it wants to. For example, online games may disable your mouse cursor during play. You can decide whether you want websites to be able to do this; the default is that they have to ask.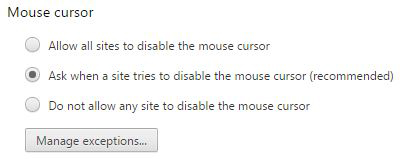 Figure 10: Tell Chrome not to let websites disable your cursor.
Figure 10: Tell Chrome not to let websites disable your cursor. Source: Google.com
Protected content
Protected content is usually content that you’ve subscribed to or purchased the right to view on your computer. If you do this often, you’ll want to make sure the Allow box is checked for this option.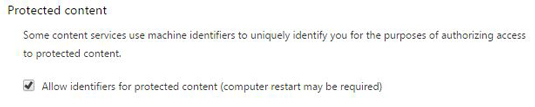 Figure 11: Make it so you can view the content you purchase.
Figure 11: Make it so you can view the content you purchase. Source: Google.com
Media
Some websites, such as sites that offer web conferencing, may want to use your microphone and camera. That’s perfectly understandable, given the usage. But beware websites that you don’t know that want access. That’s why Chrome asks for your permission before granting access. But if you’re sure you’d never want a website to have that kind of access, choose Do Not Allow from the options.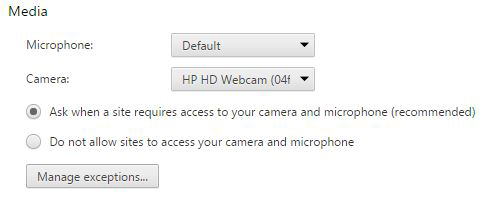 Figure 12: Don’t let sites peek at you.
Figure 12: Don’t let sites peek at you. Source: Google.com
Unsandboxed plugin access
Chrome runs all of its plug-ins in a sandboxed environment, which means that it limits the access that the plug-ins have to your computer. That way, they can’t cause all kinds of havoc on your computer. Some plug-ins, however, require unrestricted access. You can safely allow the above-board add-ons, such as a streaming video player from a company you trust (such as your cable company), to run outside of the sandboxed environment. But you should be very careful about giving that kind of access to any and all plug-ins. It’s best to let Chrome ask when to run plug-ins outside of the sandbox.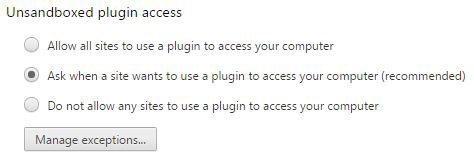 Figure 13: Keep plug-ins playing in the sandbox.
Figure 13: Keep plug-ins playing in the sandbox. Source: Google.com
Automatic downloads
Some websites may try to force Chrome to download multiple files — and some of them may be harmful. For example, if you download one file by choice, the site may try to download another file after that without your permission. Obviously, you don’t want websites downloading stuff to your computer without your permission, so it’s best to keep the Ask When option selected.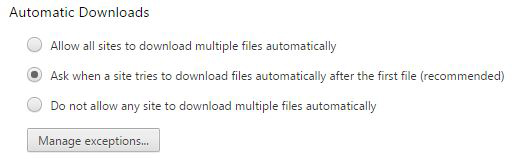 Figure 14: Prevent unauthorized downloads.
Figure 14: Prevent unauthorized downloads. Source: Google.com
MIDI devices full control
MIDI is an old technology that allows for digital communication between electronic musical instruments. What does this have to do with Chrome? Well, believe it or not, your computer contains MIDI support (and has for a long, long time). Websites can access those MIDI devices to make music in your Chrome browser. Will you ever use this? Probably not, but you might as well leave the default Ask Me option selected.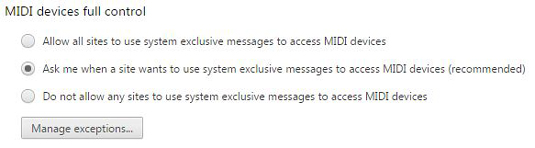 Figure 15: Allow websites to use your computer’s MIDI devices.
Figure 15: Allow websites to use your computer’s MIDI devices. Source: Google.com
Most of these settings have a Manage Exceptions button that enables you to set which sites you want to exclude from a particular exception. So, for example, if you don’t want to download images on most sites except for a few, then you can list the exceptions under that setting.






