Most network communication is sent along the network wire in cleartext, meaning that anyone connected to your network can read the information. But if the information is traveling across the Internet, anyone can view that information if it is passed in cleartext.
Most Internet protocols, such as HTTP, send information in cleartext, and it is up to the people who set up the servers that use these Internet protocols to encrypt the information before it is released to the Internet. Encrypting the information means that the information is run through a mathematical calculation that generates an altered version of the information: a result. For example, the words Glen Clarke could be encrypted to look like 7y3i s3fk4r. If anyone intercepts such encrypted information and views it while it is traveling across the wire, the information would mean nothing.
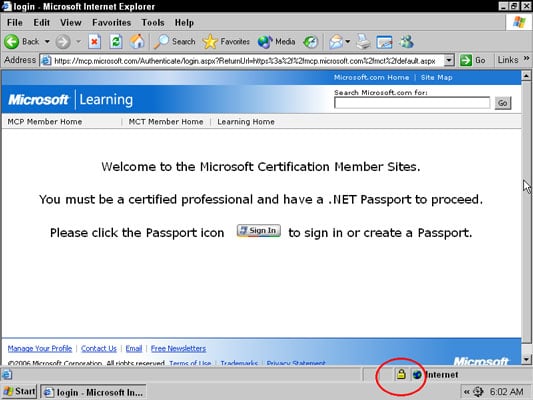
Here is a real-world example. You type your credit card number on a website, but you certainly do not want that credit card number to be viewed while you send it from your client computer to the server. You want to be sure that the website where you enter the credit card number encrypts the traffic. You can tell by the lock icon that appears in the web browser, as shown.
It is important for the A+ Exams that you understand popular methods of encrypting traffic. You can use a number of technologies, such as
- Secure Sockets Layer (SSL): This protocol is used to encrypt different types of Internet traffic. For example, you could use SSL to encrypt HTTP traffic by applying a digital certificate to the website. The digital certificate contains the key that is used to encrypt and decrypt the traffic.
- Internet Protocol Security (IPSec): This protocol can encrypt all TCP/IP traffic between systems. As a network administrator, you configure IPSec on the server and the clients with the same key or digital certificates, which are used to encrypt and decrypt network traffic. Because of the configuration, it is an unlikely solution for a website but is a great way to encrypt traffic on your network.
- Virtual Private Network (VPN): A VPN allows a user to connect across the Internet to a remote network, typically her office network, and send information between her system and the office network securely. The information is secured because the VPN technology used creates an encrypted tunnel between the user and the office network — any data that travels through the tunnel is encrypted.